A vulnerability in Microsoft's software makes it possible for an attacker to automatically forward emails from victims to their own email account, even if the Exchange server is set to not allow automatic email forwarding . That reports security company Trustwave, which speaks of a security vulnerability. Microsoft has been notified, but it is unclear if and when a solution will be released.
It is common for attackers who compromise an email account to create a forwarding rule so that incoming emails are automatically forwarded. Organizations can block automatic forwarding of e-mails to external e-mail addresses on their Exchange server. Trustwave reports that it is possible to bypass these rules through the desktop version of Outlook.
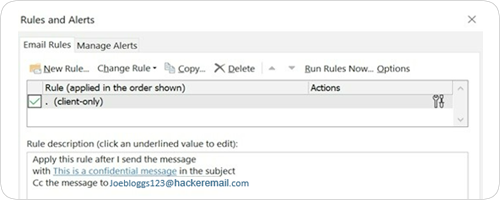
An attacker can set in the e-mail software that all sent e-mail automatically goes to an e-mail address of the attacker. This is possible via a cc rule, where the attacker's email address is automatically added as a cc with every email sent. According to Trustwave, it is unlikely that a victim would discover this.
The security company acknowledges that it is not a simple technique, as an attacker must first have access to the victim's system, for example via malware. It is therefore primarily intended as a post-exploitation technique. Microsoft has been notified of the issue. A solution is not yet available and it is unclear if and when it will be available.